Articles
How parental controls add value to fully-featured Wi-Fi router products
5 min read
Rising user expectations require advanced features in the router to stay competitive
Today’s home network users are security and privacy-conscious. They expect great Wi-Fi with high-quality broadband connectivity. Users also want to know their experience is protected and under their control. This is especially true of families with young adults and children in the household. Parents want to regulate screen time and ensure that their children will have a safe and secure experience when they are online by filtering inappropriate or dangerous content.
For this reason, “parental controls” have become an essential feature for Wi-Fi routers to implement. Manufacturers are using it as an advanced feature to differentiate their products, and service providers are offering it as a value- add to their overall packages. New startups are entering the market, offering products targeted explicitly towards families concerned with content, privacy, and security.
What are parental controls?
The term “parental controls” refers to the use cases themselves. Parents want to make sure their children are accessing safe content, and they also want to set limitations. As such, there are two main parental control features that Wi- Fi routers implement: content filtering and access restrictions. How do they work, and which technologies support them?
Content filtering
Content filtering blocks users from accessing specific web resources on the Internet, such as age-inappropriate content or dangerous resources that contain malware. Filtering makes use of lists curated by different filtering providers. These lists serve as differentiators for the manufacturer or provider that builds them, though some free and open-source solutions exist.
There are several different ways to implement content filtering.
URL filtering relies on a list of specific URLs to determine access. White- listing allows only specific URLs to be accessed, while black-listing denies access to the listed URLs.
Application filtering works very similarly to a firewall. In this case, filtering occurs on port ranges, protocol types, or other known application types.
IP filtering may filter specific ranges of IP addresses, or rely on GeoIP information to block addresses in a given region that might have a below- average reputation.
DNS based filtering is similar to URL filtering, but relies on domain classification of malicious sites and uses DNS to redirect users to a different resource at the time of the DNS lookup. For example, when the DNS filter sees a request for mybadsite.net, it instead resolves the address to a known, safe IP address (either a cloud service or local on the Wi-Fi router) where the resource delivered may be a web-portal or page that explains why the content was blocked.
Example: DNS filtering in action
Here’s an example of DNS filtering in action using OpenDNS.
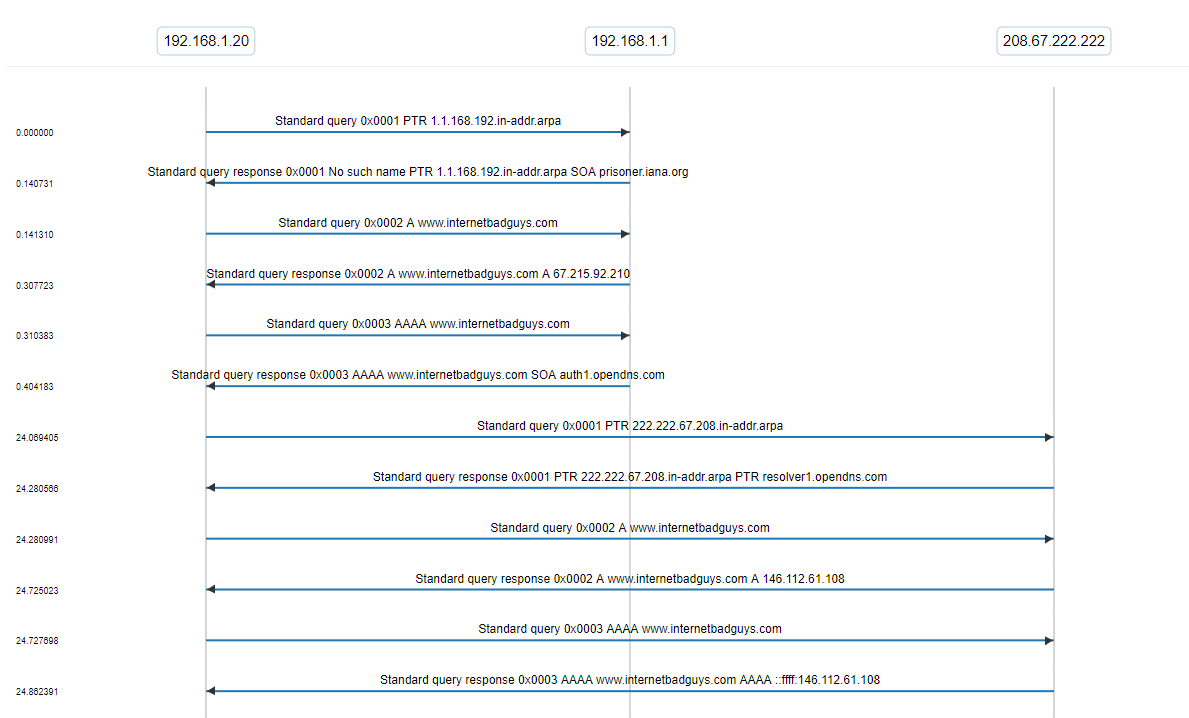
View the capture on CloudShark
In the packet capture, you’ll see that a DNS request was made using our default DNS server (in this case, the gateway at 192.168.1.1) to internetbadguys.com, a test domain for OpenDNS representing a malicious site. It responds with the authoritative answer.
When we change our DNS server to one of the OpenDNS’s servers (208.67.222.222), it changes the IP address given in the response to 146.112.61.108. In a device implementing DNS filtering or using a service like OpenDNS, it could provide some HTML content stating that the site was blocked.
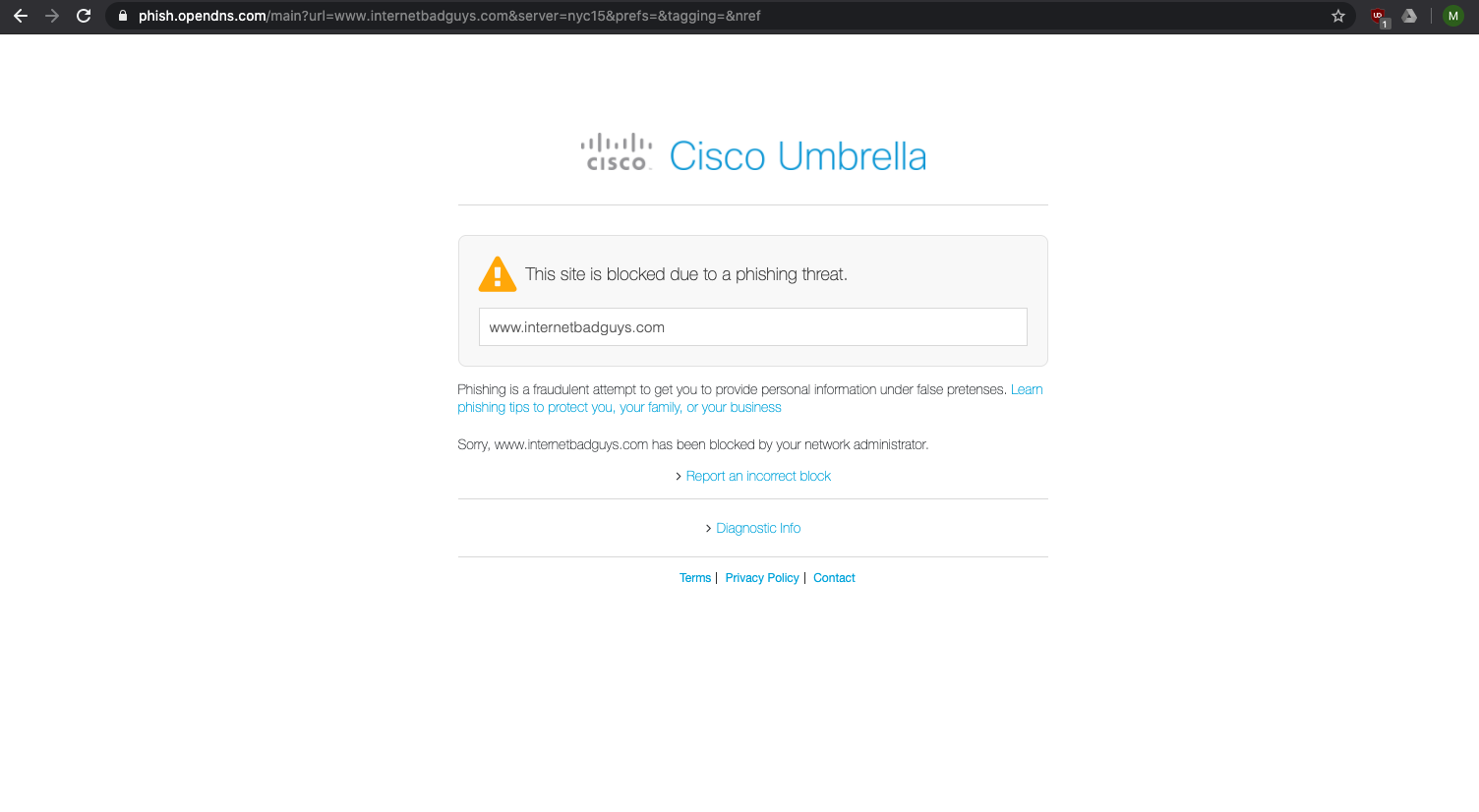
OpenDNS Phishing Warning
Internet access restrictions
Internet access restrictions limit when a user can access the Internet through the Wi-Fi router. They act like an on/off switch that denies the user access to the WAN based on particular criteria.
Usually, these criteria are time-based. Parents want to limit access to the Internet according to a set schedule or implement “screen time” limits that cause access to time out after it has reached a set amount of time.
The Wi-Fi router uses MAC address filtering to apply the limits to a specific device. Many solutions have a feature in the user interface that lists the hosts that the router has identified. Users can select which hosts to limit, and the router allows or denies access based on the device’s MAC address. For example, a parent could cap or restrict access to the Internet from a gaming console after a few hours, while allowing a student’s laptop to access the Internet for remote learning. Or, a parent could disable access for all of the child’s devices after 9:00 pm, without restricting access to other household devices. Very often, the application lets users give friendly names to each device or group them together to make it easy to apply policy.
Combining filtering with access restrictions
Many devices also provide the ability to craft more advanced policy that combines these features. Parents may want to limit some applications according to a schedule, but not all Internet traffic. For example, they could allow access only to a specific educational application during homework time, opening up general access later. Or, they could combine both schedule and time limit restrictions to give children a window in which they can spend their screen- time.
Security applications help differentiate the Wi-Fi router market
Manufacturers and providers are adding more applications to the router to give end-users a better home networking experience. Parental controls are a valuable part of a full-featured Wi-Fi router product focused on privacy and security. They give parents the flexibility they need to manage that experience for their entire family, helping them use it more safely and responsibly.
These features can be complex to design and implement, however. Companies looking to differentiate based on applications like parental controls should rigorously test these features during the development process to ensure robust and interoperable products.
CDRouter Security contains an ever-growing list of fully-automated test cases for features like these. Find out how repeatable, consistent testing can help you build better products and be first-to-market with advanced Wi-Fi routers.
Photo credit Ludovic Toinel via Unsplash